Author: 0xTodd Source: X, @BessJoyce16
Many friends still confuse FHE with ZK, MPC and other encryption technologies, so this article will compare these three technologies in detail.
Last time we analyzed how the Fully Homomorphic Encryption (FHE) technology works.
However, many friends still confuse FHE with ZK, MPC and other encryption technologies, so the second thread plans to compare these three technologies in detail:
FHE vs ZK vs MPC
First, let’s start with the most basic questions: - What are these three technologies? - How do they work? - How do they work for blockchain applications?
1. Zero-knowledge proof (ZK): Emphasis on "proof without disclosure"
The proposition explored by zero-knowledge proof (ZK) technology is: how to verify the authenticity of information without revealing any specific content.
ZK is built on a solid foundation in cryptography. Through zero-knowledge proof, Alice can prove to the other party, Bob, that she knows a secret without revealing any information about the secret itself.
Imagine a scenario where Alice wants to prove her credit to Bob, an employee of a car rental company, but she doesn't want to go to the bank to get a statement or something like that. At this time, for example, the "credit score" of a bank/payment software is comparable to her "zero-knowledge proof".
Alice proves that her credit score is good without showing her account flow under the condition of "zero knowledge" of Bob. This is zero-knowledge proof.
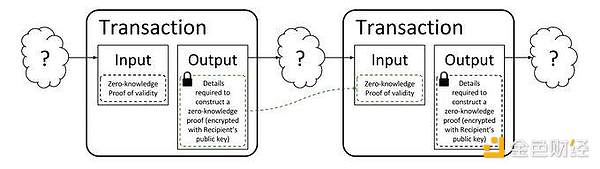
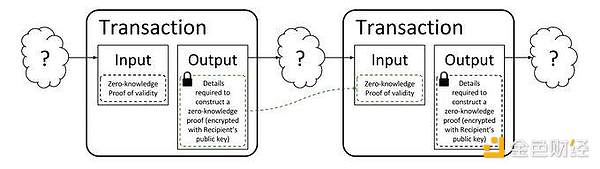
If applied to the blockchain, you can refer to the previous anonymous coin Zcash:
When Alice transfers money to others, she needs to be anonymous and prove that she has the power to transfer these coins (otherwise it will lead to double spending), so she needs to generate a ZK proof.
Therefore, after seeing this proof, miner Bob can still put the transaction on the chain without knowing who she is (i.e., zero knowledge of Alice's identity).
2. Multi-party secure computing (MPC): emphasizing "how to calculate without leaking"
Multi-party secure computing (MPC) technology is mainly used for: how to allow multiple participants to calculate together safely without leaking sensitive information.
This technology allows multiple participants (such as Alice, Bob and Carol) to complete a computational task together without any party revealing their input data.
For example, if Alice, Bob and Carol want to calculate the average salary of the three of them without revealing their specific salaries. How to do it?
Each person can divide their salary into three parts and exchange two of them with the other two people. Everyone adds up the numbers they received and then shares the result.
Finally, the three people sum up the three sums and get the average, but they cannot determine the exact salary of anyone other than themselves.
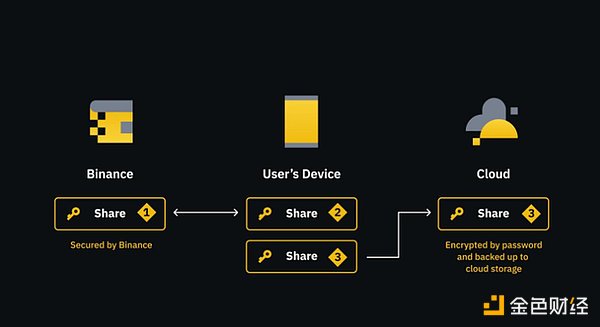
If applied to the crypto industry, MPC wallets use this technology.
Take the simplest MPC wallet launched by Binance or Bybit as an example. Users no longer need to save 12 mnemonics. Instead, it is a bit like changing the private key to 2/2 multi-signature, with one copy on the user's mobile phone, one copy on the user's cloud, and one copy on the exchange.
If the user accidentally loses his or her mobile phone, at least the cloud + exchange can still recover it.
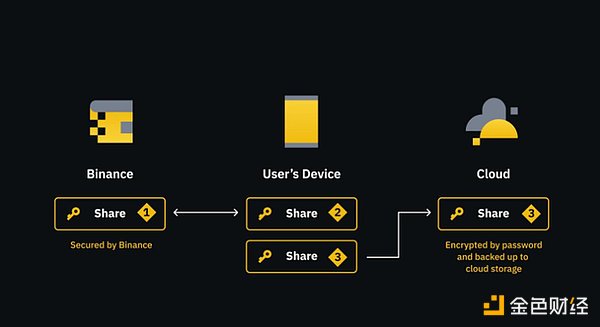
Of course, if higher security is required, some MPC wallets can support the introduction of more third parties to protect private key fragments.
Therefore, based on the cryptographic technology of MPC, multiple parties can use private keys safely without trusting each other.
3. Fully Homomorphic Encryption (FHE): Emphasis on “How to encrypt in order to outsource”
As I said in the previous thread, fully homomorphic encryption (FHE) is applied to: how do we encrypt, so that after the sensitive data is encrypted, it can be handed over to an untrusted third party for auxiliary calculation, and the result can still be decrypted by us. Portal to the previous article: https://x.com/0x_Todd/status/1810989860620226900… For example, Alice does not have computing power and needs to rely on Bob to calculate, but does not want to tell Bob the truth. Therefore, she can only introduce noise into the original data (do any number of addition/multiplication encryption), and then use Bob’s powerful computing power to process the data. Finally, Alice decrypts it herself to get the real result, while Bob knows nothing about the content.
Imagine if you need to process sensitive data, such as medical records or personal financial information, in a cloud computing environment, FHE is particularly important. It allows data to remain encrypted throughout the entire processing process, which not only protects data security but also complies with privacy regulations.
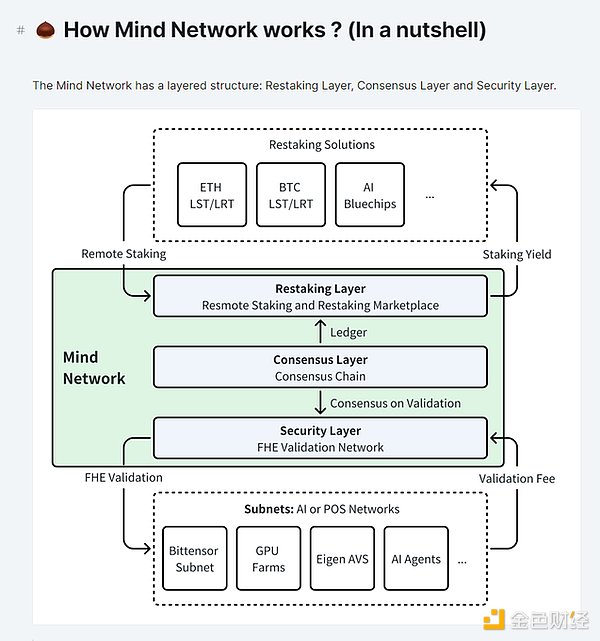
Last time, we focused on why the AI industry needs FHE. So what applications can FHE bring to the crypto industry? For example, there is a project called Mind Network that has received an Ethereum Grant, which is also a project of Binance Incubator. It focuses on a native problem of the PoS mechanism:
PoS protocols like Ethereum have 100w+ validators, so there is naturally no problem. But for many small projects, the problem comes, and miners are naturally lazy.
Why do you say that? In theory, the work of a node is to conscientiously verify whether each transaction is legal. But some small PoS protocols do not have enough nodes, and include many "big nodes".
Therefore, many small PoS nodes have found that instead of wasting time calculating and verifying by themselves, it is better to directly follow and copy the ready-made results of large nodes.
This will undoubtedly lead to very exaggerated centralization.
In addition, such as voting scenarios, there are also signs of "following".
For example, in the previous voting of the MakerDAO protocol, because A16Z had too many MKR votes at the time, its attitude often played a decisive role in certain protocols. After A16Z voted, many small votes could only be forced to follow the vote or abstain, which could not reflect the real public opinion at all.
Therefore, Mind Network uses FHE technology:
When PoS nodes *do not know* each other's answers, they can still use machine computing power to complete the verification of blocks to prevent PoS nodes from copying each other.
or
After voters *do not know* each other's voting intentions, they can still use the voting platform to calculate the voting results to prevent following the vote.
This is one of the important applications of FHE in blockchain.
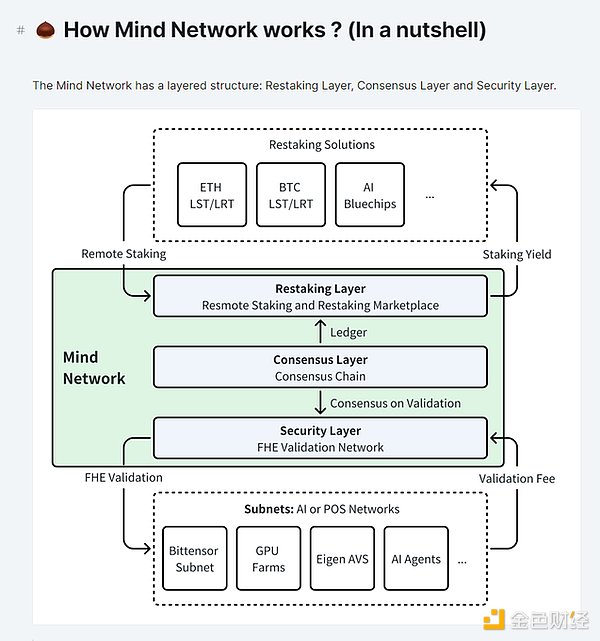
Therefore, in order to achieve such a function, Mind also needs to rebuild a re-staking nesting doll protocol. Because EigenLayer itself will provide "outsourced node" services for some small blockchains in the future, if combined with FHE, it can greatly improve the security of PoS networks or voting.
To make an inappropriate analogy, the introduction of Eigen+Mind to a small blockchain is a bit like a small country that cannot handle its own internal affairs, so it introduces foreign troops.
This is also one of the differences between Mind and Renzo and Puffer in the PoS/Restaking branch. Mind Network started later than Renzo and Puffer, and has just launched its main network recently. Relatively speaking, it is not as popular as Re-taking summer.
Of course, Mind Network also provides services in the AI branch, such as using FHE technology to encrypt data fed to AI, and then allowing AI to learn and process this data without knowing the original data. Typical cases include cooperation with the bittensor subnet.
Finally, let’s summarize:
Although ZK (zero-knowledge proof), MPC (multi-party computing), and FHE (fully homomorphic encryption) are advanced encryption technologies designed to protect data privacy and security, they differ in application scenarios/technical complexity:
Application scenario: ZK emphasizes "how to prove". It provides a way for one party to prove the correctness of a piece of information to another party without revealing any additional information. This technology is very useful when it is necessary to verify permissions or identities.
MPC emphasizes "how to calculate". It allows multiple participants to perform calculations together without revealing their respective inputs. This is in situations where data cooperation is required but the privacy of data of all parties must be protected, such as cross-institutional data analysis and financial auditing.
FHE emphasizes "how to encrypt". It makes it possible to entrust complex calculations while keeping the data encrypted at all times. This is particularly important for cloud computing/AI services, where users can safely process sensitive data in a cloud environment.
Technical complexity: Although ZK is powerful in theory, designing effective and easy-to-implement zero-knowledge proof protocols can be very complex and require deep mathematical and programming skills, such as various "circuits" that everyone does not understand.
MPC needs to solve synchronization and communication efficiency problems when implementing it, especially when there are many participants, the coordination cost and computational overhead can be very high.
FHE faces huge challenges in computational efficiency, and the encryption algorithm is relatively complex. It was not until 2009 that it was formed. Although it is very attractive in theory, its high computational complexity and time cost in practical applications are still the main obstacles.
To be honest, the data security and personal privacy protection we rely on are facing unprecedented challenges. Imagine that without encryption technology, the information in our text messages, takeouts, and online shopping processes would be exposed. Just like an unlocked door, anyone can enter at will.
I hope that friends who are confused about these three concepts can thoroughly distinguish these three pearls on the holy grail of cryptography.
 JinseFinance
JinseFinance