Claude Code's source code has been leaked.
Nearly two thousand files and over half a million lines of TypeScript code have been exposed on the public internet. This is one of the largest accidental public releases of source code among leading AI companies to date.
The developer, Chaofan Shou, was the first to discover and publicly disclose this "vulnerability."
The developer, Chaofan Shou, was the first to discover and publicly disclose this "vulnerability."
Developer @realsigridjin acted swiftly, immediately backing up the leaked source code to GitHub. The repository is named instructkr/claude-code and labeled "Claude Code Snapshot for Research". Within just two hours of its launch, the repository garnered over 50,000 stars, setting a new record for the fastest GitHub repository to reach this milestone.
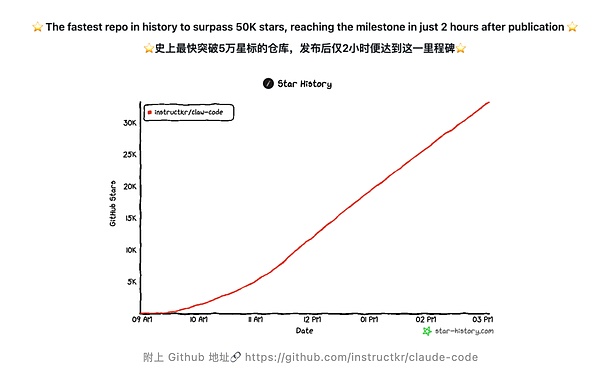
Here is the Github address: https://github.com/instructkr/claude-code
The incident stemmed from Anthropic mistakenly packaging and releasing the source map debugging files along with a Claude Code version release to a public package repository.
The incident occurred when Anthropic mistakenly packaged and released the source map debugging files to a public package repository during a Claude Code version release.
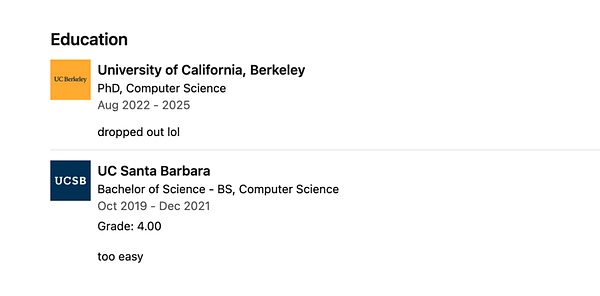
The source map file exposed the location of the original source code archive, allowing outsiders to access and download the compressed source code package in Anthropic's cloud storage. Anthropic subsequently responded that the incident was a "human error during the packaging process," not a security breach, and that no user data or credentials were leaked. Boris Cherny, the creator of Claude Code, also briefly commented on X, confirming it was simply a "developer error." After the news spread, Musk also joined in the fun, retweeting a post from a netizen jokingly saying that Anthropic is now more open than OpenAI, and leaving a comment saying "That's amazing?". It's worth mentioning that Chaofan Shou, who discovered this leak, is a Chinese security researcher with a very impressive resume. His GitHub username is shouc, and his X account is @shoucccc. According to his LinkedIn profile, he entered the University of California, Santa Barbara in 2019 to pursue a bachelor's degree in Computer Science. He completed his studies in approximately two years, graduating early with a perfect GPA of 4.0. The only note in the degree section is: "too easy".
Some netizens have done the math, which is equivalent to maintaining the intensity of preparing for the college entrance exam every semester and getting the highest score in every subject for three consecutive years.
After graduating with his bachelor's degree, he went to the University of California, Berkeley to pursue a PhD in Computer Science under the tutelage of Koushik Sen, a renowned professor in the field of program analysis. He later chose to drop out and start his own business. His LinkedIn bio is equally concise: "dropped out lol (dropped out, haha)".
He previously worked as a security engineer at Salesforce, where he was responsible for developing static code analysis tools and data pipelines. Later, he joined Veridise to lead the development of automated testing tools for smart contracts. In 2023, he co-founded Fuzzland, a Web3 security and high-frequency trading company, and served as its CTO. The company was later acquired by Solayer, where he became a full-time software engineer. His job description read "full-time larping on Twitter." In short, he was jokingly referring to himself as someone who spends all his time posting on Twitter to gain attention, and mocking himself for not doing his job properly. Fuzzland has helped recover over $30 million in stolen on-chain assets and currently protects and manages over $5 billion in assets. His flagship project on GitHub, ityfuzz, is a snapshot fuzzing tool for smart contracts and has garnered over 1,100 stars. On the academic front, his Google Scholar page shows a total of 224 citations, an h-index of 6, and an i10-index of 4. His papers have been published in top academic conferences such as CCS, ISSTA, and CoNext, and his research interests include smart contract fuzzing, web security, and distributed systems. In the bug bounty field, he has been active since 2016. The vulnerabilities he has disclosed cover well-known platforms such as Twitter, Etherscan, Devin.ai, and Google Nest, involving various high-risk issues such as account hijacking, system takeover, and user behavior leakage. He has received approximately $1.9 million in bug bounties. Over the past year, he has maintained an active pace of 1159 commits on GitHub. After this person's identity sparked widespread discussion on social media, some netizens commented in the comments section: "Is it Shou Chaofan? He's my junior from high school." Public information also seems to confirm this clue: he attended Shanghai Pinghe Bilingual School and was selected as a university publicity officer by the China Computer Federation (CCF). The screenshot is from the WeChat official account "Pinghe Education". Online, there are even teaching materials circulated with his hand-drawn illustrations to help solve AMC 10 problems. Of course, the possibility of someone with the same name cannot be ruled out. Interestingly, Anthropic presents itself as the most security-conscious AI company, and the person who exposed this facade is a Chinese programmer on GitHub who calls himself a "senior script kiddie". "Script kiddie" is a term used in hacker culture to mock those who are technically illiterate and only know how to copy tools without understanding the underlying principles. Posting this phrase prominently on one's homepage is undoubtedly just a joke. But it was precisely this person—perhaps due to professional habit—who, during a casual technical check, revealed Anthropic's 500,000 lines of source code to everyone.
 JinseFinance
JinseFinance
 JinseFinance
JinseFinance JinseFinance
JinseFinance JinseFinance
JinseFinance JinseFinance
JinseFinance JinseFinance
JinseFinance JinseFinance
JinseFinance JinseFinance
JinseFinance JinseFinance
JinseFinance Beincrypto
Beincrypto Cointelegraph
Cointelegraph